To understand security concepts, you'll likely face questions about network security, application security, and cryptography. This guide is designed to prepare you for a computer security interview. You will gain a solid understanding of essential concepts and technologies. You'll learn to understand security concepts with these 50 questions and answers.
On This Page
- Fundamental Computer Security Concepts
- What is computer security?
- What are the three main goals of computer security (CIA triad)?
- What is the difference between authentication and authorization?
- What is a firewall, and how does it work?
- Explain the concept of defense in depth.
- What is the principle of least privilege?
- What is the difference between a vulnerability and a threat?
- What is a zero-day vulnerability?
- What is social engineering?
- What is phishing?
- Network Security Fundamentals
- What is a network protocol?
- What is TCP/IP?
- What is the OSI model?
- What is a VPN (Virtual Private Network)?
- What is a DNS (Domain Name System)?
- What is a man-in-the-middle (MITM) attack?
- What is a denial-of-service (DoS) attack?
- What is a distributed denial-of-service (DDoS) attack?
- What is port scanning?
- What is network segmentation?
- Application and Software Security
- What is a buffer overflow?
- What is SQL injection?
- What is cross-site scripting (XSS)?
- What is a software vulnerability scanner?
- What is input validation?
- What is output encoding?
- What is a security patch?
- What is a security audit?
- What is penetration testing?
- What is a code review?
- What is the purpose of a security information and event management (SIEM) system?
- What is the role of a security analyst?
- What is the importance of incident response?
- What is malware?
- What is ransomware?
- What is a virus?
- What is a worm?
- What is a Trojan horse?
- What is multi-factor authentication (MFA)?
- What is a security token?
- What are the different types of encryption algorithms?
- What is symmetric encryption?
- What is asymmetric encryption?
- What is a digital signature?
- What is a certificate authority (CA)?
- What is the purpose of a security policy?
- What is a risk assessment?
- What is business continuity planning (BCP)?
- What is disaster recovery (DR)?
- What is the role of cryptography in computer security?
- Similar Problems (Quick Solutions)
- References
We Also Published
Preparing for a computer security interview can seem daunting, but with the right preparation, you can confidently demonstrate your knowledge and enthusiasm. This guide helps you to **understand security concepts** by providing a comprehensive set of frequently asked questions (FAQs) and detailed answers.
Fundamental Computer Security Concepts
Before diving into specific threats and technologies, it's crucial to grasp the basic principles that underpin all aspects of computer security. What are the key elements of a robust security posture?
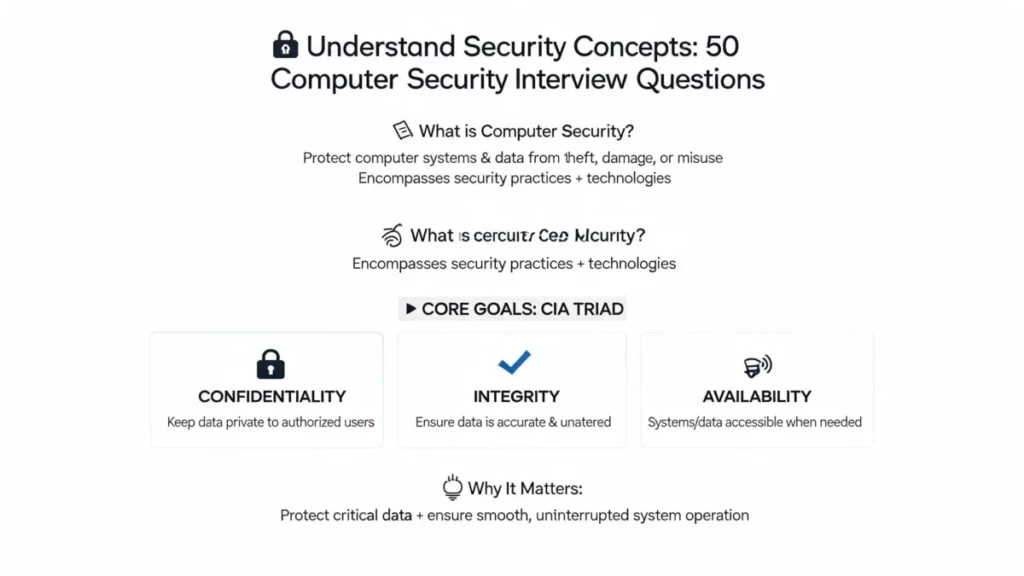
What is computer security?
Computer security involves protecting computer systems and data from theft, damage, or misuse. It encompasses a wide range of practices and technologies.
The main goals are confidentiality, integrity, and availability (CIA triad). Computer security is essential to protect data and ensure the smooth operation of systems.
This includes physical security, network security, and application security.
What are the three main goals of computer security (CIA triad)?
The CIA triad refers to Confidentiality, Integrity, and Availability. These are the three core principles.
Confidentiality ensures that only authorized individuals can access sensitive information. Integrity ensures that data is accurate and has not been tampered with.
Availability ensures that systems and data are accessible when needed. Maintaining the CIA triad is vital for a strong security posture.
What is the difference between authentication and authorization?
Authentication verifies a user's identity, while authorization determines what a user is allowed to access. Authentication confirms who a user is.
Authorization defines what resources and actions a user can perform. For example, a user authenticates with a username and password.
Then, the system authorizes the user to access specific files or perform certain tasks. Authentication precedes authorization.
What is a firewall, and how does it work?
A firewall is a network security device that monitors and controls incoming and outgoing network traffic based on predetermined security rules.
It acts as a barrier between a trusted internal network and untrusted external networks (like the internet). Firewalls inspect network packets.
They filter traffic based on rules such as source/destination IP addresses, ports, and protocols. Firewalls can be hardware or software-based.
Explain the concept of defense in depth.
Defense in depth is a security strategy that employs multiple layers of security controls to protect an asset. It is important to implement several layers.
If one layer fails, others are still in place to provide protection. This approach reduces the likelihood of a successful attack.
Examples of layers include firewalls, intrusion detection systems, antivirus software, and access controls. It is a fundamental security principle.
What is the principle of least privilege?
The principle of least privilege dictates that users and systems should only have the minimum necessary access rights to perform their required tasks.
This minimizes the potential damage from a security breach. It helps to limit the attack surface and prevent unauthorized access.
It is a crucial component of access control and helps to reduce the impact of compromised accounts.
What is the difference between a vulnerability and a threat?
A vulnerability is a weakness in a system that could be exploited by a threat. A threat is a potential danger that can exploit a vulnerability.
A vulnerability is a flaw, while a threat is a potential cause of harm. For example, a software bug is a vulnerability.
A hacker exploiting that bug is a threat. Understanding the difference is crucial for risk management.
What is a zero-day vulnerability?
A zero-day vulnerability is a security flaw that is unknown to the vendor or the public. It is a vulnerability that has not been patched.
Hackers can exploit these vulnerabilities before a patch is available. Because there is no existing fix, zero-day exploits are particularly dangerous.
Vendors race to develop and deploy patches to mitigate these threats. Zero-day attacks are difficult to defend against.
What is social engineering?
Social engineering is the art of manipulating people into divulging confidential information or performing actions that compromise security. It involves human interaction.
Attackers often use psychological tactics to trick individuals. Phishing, pretexting, and baiting are common social engineering techniques.
It is one of the most effective ways to bypass technical security controls. Training and awareness are critical for defense.
What is phishing?
Phishing is a type of social engineering attack where attackers impersonate a trustworthy entity to steal sensitive information. It usually involves emails.
Attackers often send emails that appear to be from legitimate organizations. They try to trick users into revealing usernames, passwords, or financial details.
Phishing attacks are a major threat to businesses and individuals. Being able to recognize phishing attempts is crucial.
Network Security Fundamentals
Network security protects the infrastructure that connects computer systems and devices. What are the key components of a secure network?
What is a network protocol?
A network protocol is a set of rules and standards that govern how data is transmitted between devices over a network. It is a set of rules.
Protocols define the format, timing, and sequencing of data exchange. Examples include TCP/IP, HTTP, and FTP.
Protocols ensure that devices can communicate effectively. They are essential for network functionality.
What is TCP/IP?
TCP/IP (Transmission Control Protocol/Internet Protocol) is the fundamental communication language or protocol of the Internet. It is the foundation.
It defines how data is transmitted and routed across networks. TCP/IP is a suite of protocols.
It enables reliable communication between devices. TCP/IP is essential for internet connectivity.
What is the OSI model?
The OSI (Open Systems Interconnection) model is a conceptual framework that describes how data is transmitted over a network. It is a model.
It divides the communication process into seven layers, each with specific functions. These layers are Physical, Data Link, Network, Transport, Session, Presentation, and Application.
The OSI model helps in understanding and troubleshooting network issues. Each layer performs a specific function.
What is a VPN (Virtual Private Network)?
A VPN is a secure, encrypted connection over a public network, such as the internet. It provides a secure tunnel.
It allows users to access a private network remotely while protecting their data. VPNs encrypt the data.
They are commonly used for secure remote access and to protect online privacy. VPNs are a valuable security tool.
What is a DNS (Domain Name System)?
DNS is a system that translates human-readable domain names (like example.com) into IP addresses. It's the internet's phonebook.
It allows users to access websites using easy-to-remember names. When you type a domain name, DNS translates it.
It is essential for internet navigation. DNS helps users find websites.
What is a man-in-the-middle (MITM) attack?
A man-in-the-middle (MITM) attack is a type of attack where an attacker intercepts communication between two parties. It is an interception.
The attacker secretly relays and possibly alters the communication. The attacker can eavesdrop on, or modify the conversation.
MITM attacks are a serious threat to data security and privacy. They can be difficult to detect.
What is a denial-of-service (DoS) attack?
A denial-of-service (DoS) attack is an attempt to make a machine or network resource unavailable to its intended users. It is an interruption.
Attackers flood the target with traffic, overwhelming it and preventing legitimate users from accessing it. It can disrupt online services.
DoS attacks can be launched from a single source. These are a common type of cyber attack.
What is a distributed denial-of-service (DDoS) attack?
A distributed denial-of-service (DDoS) attack is a DoS attack that uses multiple compromised systems as sources of attack traffic. It is a widespread attack.
This makes the attack more difficult to mitigate. DDoS attacks can overwhelm even robust systems.
They are a major threat to online services and businesses. DDoS attacks use a distributed approach.
What is port scanning?
Port scanning is a technique used to identify open ports on a network device. It is an investigation.
Attackers use port scanners to determine which services are running on a target system. This helps identify vulnerabilities.
Port scanning is a reconnaissance technique used before launching an attack. It reveals running services.
What is network segmentation?
Network segmentation is the practice of dividing a computer network into smaller, isolated subnets. It is a division.
This improves security by limiting the impact of a security breach. It helps to contain threats.
Segmentation restricts lateral movement within the network. It enhances overall security posture.
Application and Software Security
Application security focuses on protecting software applications from threats. How do you secure software and applications?
What is a buffer overflow?
A buffer overflow is a type of security vulnerability that occurs when a program writes data beyond the allocated memory buffer. It is an overflow.
This can overwrite adjacent memory, potentially allowing an attacker to execute malicious code. It is a serious vulnerability.
Buffer overflows are often exploited to gain control of a system. Careful coding practices can prevent it.
What is SQL injection?
SQL injection is a type of attack where an attacker inserts malicious SQL code into an input field to manipulate a database. It is an injection.
This can allow attackers to access, modify, or delete data in the database. It can lead to data breaches.
SQL injection is a major threat to web applications. Input validation is key to prevent it.
What is cross-site scripting (XSS)?
Cross-site scripting (XSS) is a type of attack where attackers inject malicious scripts into websites viewed by other users. It is a scripting attack.
These scripts can steal user cookies, redirect users, or deface websites. It can compromise user sessions.
XSS attacks are a common threat to web applications. Proper input validation and output encoding can prevent XSS.
What is a software vulnerability scanner?
A software vulnerability scanner is a tool that identifies security vulnerabilities in software applications. It is an identification tool.
These scanners automatically check for known vulnerabilities. They can help identify weaknesses.
They provide valuable information for patching and remediation. Scanners are essential for security audits.
What is input validation?
Input validation is the process of verifying that user-supplied data meets expected criteria. It is a verification process.
This helps prevent attacks like SQL injection and cross-site scripting. Input validation is essential for security.
It involves checking data type, format, and range. Input validation is a fundamental security practice.
What is output encoding?
Output encoding is the process of converting data to a safe format before it is displayed to the user. It is a conversion.
This prevents attacks like cross-site scripting. Output encoding ensures that malicious scripts are not executed.
It is an essential security practice for web applications. Output encoding protects against XSS.
What is a security patch?
A security patch is a piece of software designed to fix a security vulnerability. It is a software update.
Vendors release patches to address known security flaws. Patching is essential for maintaining a secure system.
Regular patching is a critical security practice. Patches fix security holes.
What is a security audit?
A security audit is a systematic assessment of an organization's security posture. It is an assessment.
Audits identify vulnerabilities, weaknesses, and compliance gaps. They can be internal or external.
Security audits help organizations improve their security. They provide valuable insights.
What is penetration testing?
Penetration testing, also known as ethical hacking, involves simulating attacks to identify vulnerabilities in a system. It is a simulation.
Penetration testers use the same tools and techniques as malicious attackers. They aim to find security flaws.
Penetration testing helps organizations improve their security posture. It provides valuable insights.
What is a code review?
A code review is a systematic examination of source code to identify vulnerabilities, bugs, and coding style issues. It is an examination.
Code reviews can be performed manually or with automated tools. They help improve software quality.
Code reviews are essential for secure software development. They help find and fix vulnerabilities.
What is the purpose of a security information and event management (SIEM) system?
A SIEM system is designed to collect and analyze security-related data from various sources to detect and respond to security incidents. It is a data management tool.
SIEM systems aggregate log data from different sources such as firewalls, intrusion detection systems, and servers. They correlate events.
This enables security teams to identify threats and respond to them. SIEM systems are crucial for threat detection.
What is the role of a security analyst?
A security analyst monitors, analyzes, and responds to security incidents. They are the front line.
They work to protect an organization's computer systems and data. Security analysts are often responsible for incident response.
They help to identify and mitigate threats. Security analysts perform various tasks.
What is the importance of incident response?
Incident response is a set of procedures and processes used to identify, contain, and recover from security incidents. It is a process.
It minimizes damage and ensures a swift return to normal operations. Incident response is essential for business continuity.
It helps organizations to mitigate the impact of security breaches. Incident response is crucial.
What is malware?
Malware, short for malicious software, is any software designed to disrupt, damage, or gain unauthorized access to a computer system. It is malicious.
Examples include viruses, worms, Trojans, and ransomware. Malware can cause significant damage.
Malware can steal data, disrupt operations, and demand ransom. Malware is a major threat.
What is ransomware?
Ransomware is a type of malware that encrypts a victim's files and demands a ransom payment to restore access. It is a demand.
Ransomware attacks are becoming increasingly common. The goal is to extort money.
Ransomware can cause significant financial and operational damage. Prevention and backups are key.
What is a virus?
A computer virus is a type of malware that attaches itself to other files and spreads to other systems. It is an attachment.
Viruses often require user action to spread. They can cause data loss and system damage.
Viruses can disrupt system operations. Antivirus software is essential for protection.
What is a worm?
A computer worm is a type of malware that self-replicates and spreads across a network without user interaction. It is a self-replicator.
Worms can spread rapidly, causing significant disruption. They exploit vulnerabilities.
Worms can consume network bandwidth and resources. They spread autonomously.
What is a Trojan horse?
A Trojan horse is a type of malware disguised as a legitimate program. It is a disguise.
It tricks users into installing it. Once installed, it can perform malicious actions.
Trojans can be used to steal data or install other malware. Trojans are a common threat.
What is multi-factor authentication (MFA)?
Multi-factor authentication (MFA) requires users to provide multiple forms of verification to access a system. It is multiple factors.
This typically includes something you know (password), something you have (phone), and something you are (biometrics). MFA adds an extra layer of security.
MFA significantly reduces the risk of unauthorized access. MFA is a best practice.
What is a security token?
A security token is a physical or digital device used to provide an additional layer of authentication. It is an authenticator.
These tokens generate a unique code that the user enters along with their password. They are used in multi-factor authentication.
Security tokens enhance security by requiring something you have. Security tokens add an extra layer.
What are the different types of encryption algorithms?
Encryption algorithms are mathematical functions used to encrypt and decrypt data. They are mathematical tools.
There are two main types: symmetric and asymmetric. Symmetric encryption uses the same key for encryption and decryption.
Asymmetric encryption uses a key pair: a public key for encryption and a private key for decryption. Encryption protects data.
What is symmetric encryption?
Symmetric encryption uses the same key to encrypt and decrypt data. It is a shared key.
It is generally faster than asymmetric encryption but requires secure key exchange. Examples include AES and DES.
Symmetric encryption is suitable for encrypting large amounts of data. It is fast and efficient.
What is asymmetric encryption?
Asymmetric encryption uses a pair of keys: a public key for encryption and a private key for decryption. It is a key pair.
The public key can be shared, while the private key must be kept secret. Examples include RSA and ECC.
Asymmetric encryption is used for secure key exchange and digital signatures. It is secure.
What is a digital signature?
A digital signature is an electronic signature used to verify the authenticity and integrity of a digital document. It is a verification tool.
It uses asymmetric encryption to ensure that the document has not been altered and that the sender is who they claim to be. It provides non-repudiation.
Digital signatures are used in various applications, such as software distribution and e-commerce. It guarantees authenticity.
What is a certificate authority (CA)?
A certificate authority (CA) is a trusted entity that issues digital certificates. It is a trusted issuer.
These certificates verify the identity of websites and individuals. CAs ensure trust in online communications.
CAs are essential for securing online transactions. They issue digital certificates.
What is the purpose of a security policy?
A security policy is a document that outlines an organization's security rules, guidelines, and procedures. It is a guide.
It provides a framework for protecting information assets. It ensures that security practices are consistent.
A security policy is essential for establishing and maintaining a strong security posture. It is a key element.
What is a risk assessment?
A risk assessment is a process of identifying, analyzing, and evaluating potential threats and vulnerabilities to an organization's assets. It is an evaluation.
It helps organizations prioritize security efforts. It helps to understand the risks.
Risk assessments are crucial for developing effective security strategies. Risk assessments are essential.
What is business continuity planning (BCP)?
Business continuity planning (BCP) is the process of creating a plan to ensure that an organization can continue its critical business functions during and after a disaster. It is a plan.
It includes measures to recover from disruptions. BCP minimizes downtime.
BCP is essential for maintaining business operations. BCP is crucial.
What is disaster recovery (DR)?
Disaster recovery (DR) is the process of restoring IT systems and data after a disaster. It is a restoration.
It focuses on minimizing downtime and data loss. DR is a critical part of business continuity.
DR ensures that an organization can recover from disasters. DR is essential.
What is the role of cryptography in computer security?
Cryptography is the practice and study of techniques for secure communication in the presence of third parties. It is a study.
It involves using mathematical algorithms to encrypt and decrypt data. Cryptography ensures confidentiality, integrity, and authenticity.
Cryptography is fundamental to modern computer security. Cryptography is crucial.
Similar Problems (Quick Solutions)
What is the difference between a hash and encryption?
Hashing creates a unique fingerprint, while encryption transforms data for confidentiality.
What is the difference between a worm and a virus?
Worms self-replicate and spread, while viruses require a host file.
What is the purpose of a security token?
To provide an additional factor for authentication.
What is the CIA triad?
Confidentiality, Integrity, and Availability.
What is the principle of least privilege?
Granting only necessary access rights.
References
These FAQs offer a starting point for your computer security journey. By understanding these concepts, you can confidently discuss key security principles. Continue studying and stay informed about the latest threats and technologies to excel in your computer security career.
| Question | Answer |
|---|---|
| What is computer security? | Protecting computer systems and data from theft, damage, or misuse. |
| What are the three main goals of computer security (CIA triad)? | Confidentiality, Integrity, and Availability. |
| What is the difference between authentication and authorization? | Authentication verifies identity; authorization grants access. |
| What is a firewall, and how does it work? | A network security device that monitors and controls network traffic. |
| Explain the concept of defense in depth. | Employing multiple layers of security controls. |
| What is the principle of least privilege? | Granting users only the minimum necessary access rights. |
| What is the difference between a vulnerability and a threat? | Vulnerability is a weakness; a threat is a potential danger. |
| What is a zero-day vulnerability? | A security flaw unknown to the vendor or the public. |
| What is social engineering? | Manipulating people to divulge confidential information. |
| What is phishing? | A type of social engineering where attackers impersonate a trustworthy entity. |
| What is a network protocol? | A set of rules governing data transmission over a network. |
| What is TCP/IP? | The fundamental communication language of the Internet. |
| What is the OSI model? | A framework describing how data is transmitted over a network. |
| What is a VPN (Virtual Private Network)? | A secure, encrypted connection over a public network. |
| What is a DNS (Domain Name System)? | Translates domain names into IP addresses. |
| What is a man-in-the-middle (MITM) attack? | An attack where an attacker intercepts communication. |
| What is a denial-of-service (DoS) attack? | Making a resource unavailable to its users. |
| What is a distributed denial-of-service (DDoS) attack? | A DoS attack using multiple compromised systems. |
| What is port scanning? | Identifying open ports on a network device. |
| What is network segmentation? | Dividing a network into smaller, isolated subnets. |
| What is a buffer overflow? | Writing data beyond the allocated memory buffer. |
| What is SQL injection? | Inserting malicious SQL code into input fields. |
| What is cross-site scripting (XSS)? | Injecting malicious scripts into websites. |
| What is a software vulnerability scanner? | A tool that identifies security vulnerabilities. |
| What is input validation? | Verifying that user-supplied data meets criteria. |
| What is output encoding? | Converting data to a safe format before display. |
| What is a security patch? | Software designed to fix a security vulnerability. |
| What is a security audit? | A systematic assessment of an organization's security posture. |
| What is penetration testing? | Simulating attacks to identify vulnerabilities. |
| What is a code review? | Examining source code to identify vulnerabilities. |
| What is the purpose of a security information and event management (SIEM) system? | To collect and analyze security-related data to detect and respond to security incidents. |
| What is the role of a security analyst? | Monitors, analyzes, and responds to security incidents. |
| What is the importance of incident response? | To identify, contain, and recover from security incidents. |
| What is malware? | Software designed to disrupt or damage systems. |
| What is ransomware? | Malware that encrypts files and demands a ransom. |
| What is a virus? | Malware that attaches to other files and spreads. |
| What is a worm? | Malware that self-replicates and spreads. |
| What is a Trojan horse? | Malware disguised as a legitimate program. |
| What is multi-factor authentication (MFA)? | Requiring multiple forms of verification. |
| What is a security token? | A device used for additional authentication. |
| What are the different types of encryption algorithms? | Symmetric and asymmetric encryption. |
| What is symmetric encryption? | Using the same key to encrypt and decrypt. |
| What is asymmetric encryption? | Using a key pair for encryption and decryption. |
| What is a digital signature? | Verifying the authenticity of a digital document. |
| What is a certificate authority (CA)? | An entity that issues digital certificates. |
| What is the purpose of a security policy? | Outlining an organization's security rules. |
| What is a risk assessment? | Identifying and evaluating potential threats. |
| What is business continuity planning (BCP)? | Ensuring business functions continue during a disaster. |
| What is disaster recovery (DR)? | Restoring IT systems after a disaster. |
| What is the role of cryptography in computer security? | Ensuring secure communication. |
RESOURCES
- 5 data security concepts you need to know - Check Point Blog
- 3 Understanding Web Service Security Concepts - Oracle Help Center
- Security concepts in Microsoft Dataverse - Power Platform
- Understanding security mistakes developers make - USENIX
- 5 Security Concepts Every Developer Should Understand
- ARINC811: 811 Commercial Aircraft Information Security Concepts ...
- IBM i security concepts
- Understand the Security Concepts of Information Assurance - LinkedIn
- ISC2 : CIC : Chapter 1 : Security Principles : Notes | by Aditya Yadav
- Need help understanding a database security concept : r/cissp
- Security Hub concepts - AWS Documentation
- ALASKAN INUIT FOOD SECURITY CONCEPTUAL FRAMEWORK:
- What's a must read book for Cyber Security? : r/cybersecurity - Reddit
- CompTIA Security+ - Maryville Works
- About Us - Personal Security Concepts, LLC
From our network :
- The Diverse Types of Convergence in Mathematics
- How to secure postgres connections across VPC, VPN, and cloud
- JD Vance Charlie Kirk: Tribute and Political Strategy
- How to design postgres partitions with native and hash methods
- Bitcoin price analysis: Market signals after a muted weekend
- Limit Superior and Inferior
- How to migrate to postgres using logical replication and cutover
- Bitcoin Hits $100K: Crypto News Digest
- Limits: The Squeeze Theorem Explained